I've had this conversation with probably 30 IT directors in the last year. They're running M365, maybe some Azure workloads, and someone tells them they need a SIEM. So now they're staring at Sentinel, Splunk, and Elastic wondering which one won't bankrupt them. Here's what I tell them.
Ingestion Cost Breakdown
We ran the numbers for a 500-user E5 org ingesting ~50 GB/day. The gap is bigger than most people expect:
Microsoft Sentinel
$25K–40K USD/year
After E5 free-tier credits do the heavy lifting
Splunk Cloud
$75K–110K USD/year
Yes, really. Standard ingest license.
Elastic Cloud
$35K–55K USD/year
Managed deployment — decent middle ground
Elastic Self-Hosted
$15K–25K USD/year
Cheapest, but you're the SRE team now
This is the part people miss
M365 E5 and Defender licenses include free ingestion for the data sources that matter most — Entra ID sign-in logs, Defender for Endpoint alerts, Office 365 audit logs, and Defender for Cloud Apps. You're already paying for E5. Sending those same logs to Splunk and paying again for ingestion is literally paying twice for data you already own.
Detection Rules and Analytics
Microsoft Sentinel
Solid MITRE ATT&CK coverage out of the box, especially for Microsoft-specific attack chains. KQL takes some getting used to if you're coming from SPL, but it's not as bad as people make it sound.
Splunk
Splunk's detection library is genuinely better. Full stop. Security Essentials and ESCU are massive. But you're paying $90K USD/year for it. That's the trade-off.
Elastic Security
Community-maintained, open-source rules. They ship fast, but quality control is hit-or-miss. Great if you've got engineers who like to tinker.
SOAR Capabilities
Detections are nice. Detections that automatically isolate a compromised laptop at 2 AM while your team is sleeping? That's where SOAR earns its keep.
Sentinel
Logic Apps playbooks are baked right in. 200+ templates, Graph API can disable a user in under 3 seconds, and it's included in your license. This is Sentinel's underrated superpower.
Splunk SOAR
Honestly the most capable SOAR platform out there. 350+ integrations. But it's a separate product with a separate bill — $25K–75K USD/year on top of what you're already paying. Ouch.
Elastic
Basic response actions, but let's be real — most Elastic shops end up bolting on Tines, Shuffle, or XSOAR. That's more integration work and more cost.
Native Microsoft Integration
This is Sentinel's trump card, and it's not close. One-click connectors. No agents to deploy. No forwarders to maintain. No syslog servers to babysit:
Meanwhile, third-party SIEMs need Azure Event Hubs, diagnostic settings configured on every single subscription, and API integrations that break every time Microsoft changes their schema. We've seen it happen. It's not fun to troubleshoot at 6 AM.
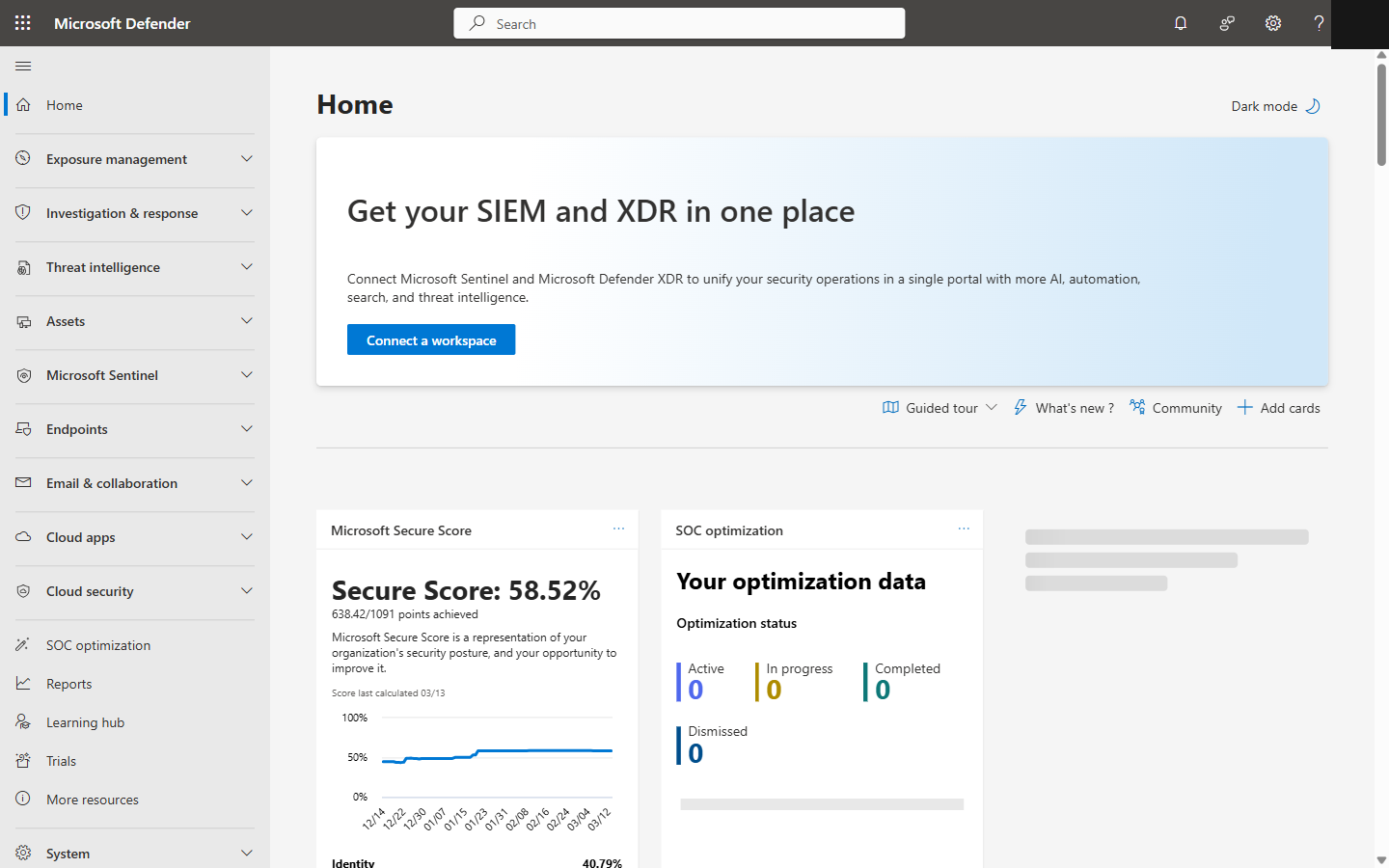
Microsoft Defender portal showing Sentinel in the navigation alongside Endpoints, Email, and Cloud Apps
Full Comparison
| Feature | Sentinel | Splunk ES | Elastic |
|---|---|---|---|
| Deployment | Cloud-native | Cloud or self-hosted | Cloud or self-hosted |
| Annual cost (500 users) | ~$30K USD | ~$90K USD | ~$45K USD |
| M365 free ingestion | Yes (E5) | No | No |
| Detection rules | 300+ | 1,400+ | 1,000+ |
| SOAR included | Yes (Logic Apps) | Separate product | Limited |
| M365 connectors | One-click | Event Hubs/API | Elastic Agent + API |
| Multi-cloud | Good | Excellent | Good |
| Community | Content Hub | Splunkbase (massive) | Open-source |
When Third-Party SIEMs Actually Make More Sense
The Bottom Line
Stop asking "Sentinel or Splunk?" Wrong question. Ask "what percentage of my stack is Microsoft?" Above 60%? Sentinel. It's cheaper, it's faster to deploy, and the native integration is genuinely hard to beat. Below 40%? Splunk or Elastic deserve a serious look on their own merits. Here's my advice: start with Sentinel, connect your Microsoft sources, turn on the built-in analytics. Give it 90 days. If you find real gaps, then talk about a hybrid approach. Most orgs never need to.